Do you know that you can remove virus from PC without formatting? In this article we will show you the best ways to do it correctly, without suffering the annoying loss of information.

An effective way to safeguard information.
Remove virus from PC without formatting
If you want to know how remove virus from PC without formatting, you are in the right place, because here we will tell you how to achieve it without losing information. However, before entering the matter, it is important that we remember some basic associated aspects, these are:
Virus
In general, we can say that a computer virus is a program, or a part of it, specially designed to cause intentional damage to the operation of a computer. Additionally, it has the function of reproducing and spreading in an accelerated way, in such a way that it can infect a greater number of elements within the same computer system.
On the other hand, in addition to viruses, we have Trojans, which are a kind of malicious code that seeks to indirectly damage the computer. In other words, they become the mediator between an infected computer and a computer; they also have the ability to spread through the generation of various copies.
For more information on this important topic, you can read the article titled: The five most dangerous viruses in history, in which you will find all the details about each of them.

Viruses: Program designed to cause damage to the functioning of computers.
Evolution of viruses
Generally speaking, computer viruses emerged in the early 80s, shortly after the official launch of personal computers. However, it is important to note that the first viruses were technological experiments, the purpose of which was to demonstrate the talent of their creators.
In this regard, since their inception, computer viruses have been compared to biological viruses, especially for their ability to reproduce and spread rapidly. However, the idea of a program coded in a specific programming language, which was capable of causing serious damage to computers, quickly spread worldwide.
However, years later the world realized that malicious code was older than previously thought. Recognizing at that time the previous existence of a project called: Creeper experimental program, which is considered today as the precursor of computer viruses.
Additionally, in the same decade of the 80 there had been another attempt, this time it was a virus called Elk Cloner. As a curious fact, we can mention that said virus, which managed to leave the laboratory where it had been created, was the result of a joke between friends.
However, it was not until several years later that the first technical details that supported the design of computer viruses were presented. It was then that subsequent creations of malicious code programs were given credit.
Finally, from those first technological demonstrations we move on to the viruses that we know today. In this regard, we can say that they are increasingly harmful and lethal in relation to the operation of computers.
Damage caused by viruses
The magnitude of the damage caused by viruses largely depends on their scope. However, in general, we can say that a virus is capable of erasing all the information contained in a computer, blocking functions or programs of the operating system, denying access to the equipment, among others.
Additionally, I invite you to watch the following video in which you will find information related to the evolution of computer viruses.
Informatic security
In general terms, computer security is responsible for minimizing the risks related to information, users, and the infrastructure of a computer system. However, in accordance with the topic at hand, we will focus only on vulnerabilities associated with information on a computer.
In this way, when we talk about remove virus from PC without formattingWe are referring to a way to mitigate the risk caused by the loss of information. Consequently, the actions that we will describe correspond to a way of guaranteeing the security of the same.
How do computers get infected?
One of the first causes of virus infections on computers is the absence of passwords or, on the contrary, their weakness. In this regard, it is important to clarify that there are three types of essential keys: access to the BIOS, access to the operating system and the screensaver of the operating system.
On the other hand, the NetBIOS protocol is another factor that causes viruses, because although it is invisible, it is generally connected to port 139. In this way, it is possible for a virus to enter the computer when we share files and printers in this way, through from Internet.

Viruses travel primarily via webmail.
Additionally, we have viruses from emails, especially those from Web mail, which is less reliable and secure. In this regard, it is important to note that most of the security violations related to this concept occur through intrusion through security questions.
Similarly, when the computer does not have antispam filters, the possibility of virus infection increases. The same happens when the antivirus of the computer is outdated or is not suitable for each type of virus.
On the other hand, a strong source of virus infection is constituted by information storage units, understood as hard drives, pen drives, among others. In the same way, Bluetooth and WiFi type connections contribute highly to the possibility that our equipment ends up being infected by viruses.
What does it mean to remove PC viruses without formatting?
As we have said, remove virus from PC without formatting it is a way of mitigating risk; however it is also a method of intrusion detection. In this regard, the primary purpose of this mechanism is to detect the exact point where the attack occurred, as well as to identify all kinds of activity that is considered suspicious.
In this same vein, it is important to clarify that an intrusion is any illegal action or activity that is committed against any resource of a computer system. In this regard, in most cases, these activities are considered dishonest and devoid of any type of authorization.
How to remove viruses from PC without formatting?
As we have seen, the viruses that infect our computers can originate from various causes. Thus, it is logical to think that there are also several ways to eliminate PC viruses without formatting, among them we have the following:
Use of antivirus and anti Trojans
Surely the first thing that comes to mind when we think of remove virus from PC without formatting, is to use an antivirus that is efficient. However, few people know that it is best to install two different types of them, as long as they do not conflict between them.

It is important to have an efficient and up-to-date virus.
In this way, one antivirus takes care of the routine scan and the other of the detection of so-called dormant viruses. Consequently, it is very possible that viruses are eliminated, but sometimes they are capable of mutating and attacking the antivirus itself.
If this is the case, an efficient way to remove virus from PC without formatting It is then the computer boot in safe mode with networking. In this way, we can perform a deeper scan from the Web, reducing the possibility of the virus infiltrating some important module on the computer.
On the other hand, just as we have looked for the solution to eliminate viruses, we must think about the best way to kill Trojans. Therefore, the most advisable thing is to install a program specialized in the detection of malicious code; however, a firewall is also important.
In this regard, a firewall is a kind of virtual blocker that stands between the computer and the network. In this way, when a Trojan manages not to be detected, the virtual wall is in charge of limiting its possible access.
Manual virus removal, without antivirus
In reality, it is not always possible to have a timely antivirus or, in some cases, the one we have is out of date. In this way, if this is our case, we must not lose our minds, because we can manually eliminate PC viruses without formatting.
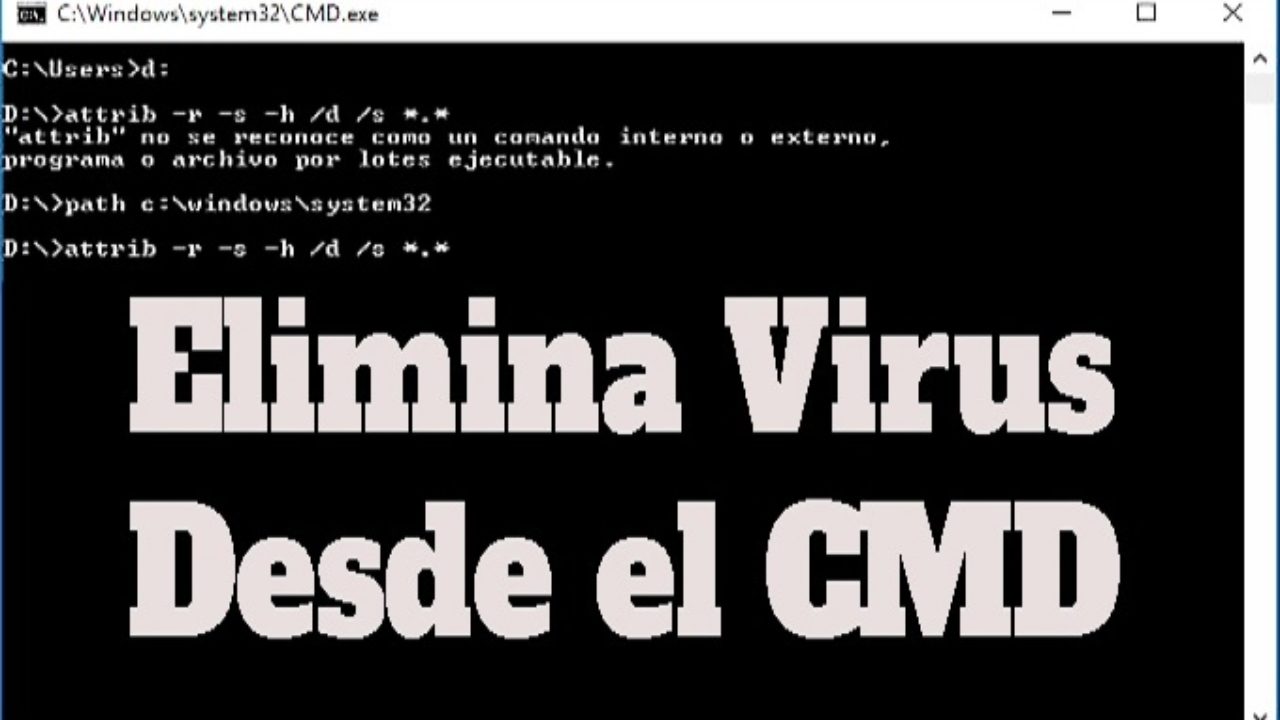
Command virus removal.
Therefore, the only requirement we need is to have basic computer knowledge and a little patience, since viruses or malware tend to present themselves in many different ways. Now, having said that, we will now describe the process to follow.
First, we must identify the location of the virus that has infected our computer. To do this, we look for the registry of system entries, which are usually automatically modified every time the malware runs on our computer.
In this regard, it is necessary to use the command Logo Win + R, which opens the box corresponding to Run. Next, we write: msconfig and press the Enter key.
The next window shows us a list with all the programs, applications and services that are executed automatically every time the computer starts up. In this way, within the options related to the services we verify if there is any name that seems suspicious to us.
In this regard, if that is the case, we copy and paste the name into the Google search bar, hoping that it identifies it as a virus or as a normal system service. In the first case, the next thing is to disable the automatic start option.
Finally, another effective method is to go to the System Task Manager and within it stop the execution of the process. However, according to the nature of the virus, these actions may not be sufficient, if so, we must restart the computer in safe mode.
Removal of virus infected files
Generally speaking, some viruses are designed to go unnoticed when searched manually. In this regard, this type of file can be confused with a hidden file or with one belonging to the system.

Eliminate the problem at the root.
If so, the option we have is to go to Windows Explorer and look in the menu for the option corresponding to Tools. Once there, we go to the Folder Options and click where it says Show hidden files and folders.
Next, we uncheck the box called: Hide protected files from the system. Later, we can search for the infected file in the usual way until we delete it, making sure to delete it from the recycle bin as well.
Using Microsoft Defender
It is no secret to anyone that the most widely used operating system on personal computers is Microsoft Windows. In this way, it is no surprise that our last option to remove viruses from PC without formatting is precisely Microsoft Defender.

A security and data protection program for Windows.
In this regard, we have that Microsoft Defender is clearly a tool for data protection, which is responsible for detecting and isolating any type of spyware. In other words, it is an antivirus program and even antispyware, which is installed by default in the most recent versions of Windows.
In addition to its normal functions as a security program, Microsoft Defender offers the user the opportunity to notify about any spyware threat. In such a way that the immediate response by the system is the installation of all the applications and device drivers necessary to automatically prevent said attack.
Microsoft Defender Features
Generally speaking, Microsoft Defender is a multifunctional tool that ensures data security by offering certain services. In this regard, these can be considered as its main characteristics: Immediate protection analysis, compatibility with Internet Explorer and development of exploration software.
Similarly, in the following video you can learn a little more about the benefits of Microsoft Defender.
https://youtu.be/zdxzHX16gWQ?t=2
How can we recognize that our PC has been infected by viruses?
As a consequence of the intrusion detection method that we have just mentioned, we have three basic ways of recognizing that our computer has been infected by viruses. From a technical point of view, these can be described as follows:
Access pattern review
The access pattern review consists of the detailed analysis of the user login times to the system. In such a way that we can identify if the accesses always occur at the same time, or if it is the same user constantly accessing the same module or service.
Transaction review
On the other hand, the review of the transaction refers to the identification of the file that has been tried to upload or download repeatedly during the number of strange accesses that have been detected. In other words, if the attacker's objective is to climb or, on the contrary, steal specific information, it is normal for them to make several attempts before achieving it, thus exposing their objective.
Automatic blocking
Automatic locking is the final stage of the intrusion detection mechanism. This basically refers to the activation of an emergency blocking system, which prevents the culmination of the computer attack to which we are being subjected.

If your computer is running slow, it freezes on its own, or it just behaves strangely. it is surely infected by viruses.
Finally, there are clear symptoms of virus infection when the computer suddenly starts behaving strangely. Thus, the slowness in the operation of the computer, the appearance of pop-up windows independently, the impossibility of accessing our account, among others, are signs of the existence of computer viruses.
General recommendations
In accordance with all that has been said above, we dare to make a series of final recommendations. Among them, the following:

The best way to prevent virus infection is to comply with computer security regulations.
Install one of these two antiviruses: Karpersky or NOD 32, which despite being designed to attack normal viruses, can somehow also counteract the effects of some Trojans. In addition, it is important to ensure that we have a true antitrojan program, which may well be The Cleaner.
Additionally, if we resort to the option of performing a scan from the Web, Panda is one of our best alternatives in this regard. However, you can choose any other program that suits your needs.
On the other hand, it is important to activate the antispam tools; in such a way that they prevent the reception of unwanted emails, which are usually carriers of serious viruses. Additionally, we must get used to safeguarding all our sensitive information, in such a way that intruders cannot access it.
Finally, I invite you to read our article called: Computer security standards on the web, where you will find all the information related to the types of computer viruses and much more.